Note
Access to this page requires authorization. You can try signing in or changing directories.
Access to this page requires authorization. You can try changing directories.
When you access resources like repositories or Azure resources during the customization process, you need to authenticate securely. You can reference Azure Key Vault secrets in your customization files to avoid exposing sensitive information, and you can use service principals to authenticate to Azure for secure resource access. This article explains how to manage and access resources securely during dev box customization.
Use key vault secrets in customization files
Use secrets from Azure Key Vault in your YAML customizations to clone private repositories or run tasks that require an access token. For example, in a customization file, use a personal access token (PAT) stored in Azure Key Vault to access a private repository.
Both team and user customizations support fetching secrets from a key vault. Team customizations, which use image definition files, define the base image for the dev box with the image parameter, and list the tasks that run when a dev box is created. User customizations list the tasks that run when a dev box is created.
To use a secret, like a PAT, in your customization files, store it as a key vault secret. The following examples show how to reference a key vault secret in both types of customizations.
Configure key vault access for customizations
To configure key vault secrets for use in your team or user customizations, make sure the Dev Center project's managed identity has the Key Vault Secrets User role on your key vault.
If your key vault is private, let trusted Microsoft services bypass the firewall because Dev Center doesn't yet support service tags.
The following screenshot shows the option to allow trusted Microsoft services to bypass the firewall in Azure Key Vault settings.
To learn more about how to let trusted Microsoft services bypass the firewall, see Configure Azure Key Vault networking settings.
Additional configuration for user customizations
To configure key vault secrets for user customizations, also:
- Ensure the Dev Center project's managed identity has both the Key Vault Reader and Key Vault Secrets User roles on your key vault.
- Grant the Key Vault Secrets User role for the secret to each user or group who needs it during dev box customization, including the Dev Center managed identity, admin accounts, and any other required users or groups.
Team customizations example
This syntax uses a key vault secret (PAT) in an image definition file. The KEY_VAULT_SECRET_URI is the URI of the secret in your key vault.
$schema: "<SCHEMA_VERSION>"
name: "<IMAGE_DEFINITION_NAME>"
image: "<BASE_IMAGE>"
description: "<DESCRIPTION>"
tasks:
- name: <TASK_NAME>
description: <TASK_DESCRIPTION>
parameters:
repositoryUrl: <REPOSITORY_URL>
directory: <DIRECTORY_PATH>
pat: "{{<KEY_VAULT_SECRET_URI>}}"
This example uses the git-clone task:
$schema: "1.0"
name: "example-image-definition"
image: microsoftvisualstudio_visualstudioplustools_vs-2022-ent-general-win11-m365-gen2
description: "Clones a public example Git repository"
tasks:
- name: git-clone
description: Clone this repository into C:\workspaces
parameters:
repositoryUrl: https://github.com/example-org/example-repo.git
directory: C:\workspaces
pat: "{{https://contoso-vault.vault.azure.net/secrets/github-pat}}"
Or, you can reference the secret in-line with a built-in task, as shown in the following example:
$schema: "1.0"
name: "example-image-definition"
image: microsoftvisualstudio_visualstudioplustools_vs-2022-ent-general-win11-m365-gen2
description: "Clones a public example Git repository"
tasks:
- name: git-clone
description: Clone this repository into C:\Workspaces
parameters:
command: MyCommand –MyParam "{{KEY_VAULT_SECRET_URI}}"
User customizations example
User customizations let you obtain an Azure DevOps token to clone private repositories without explicitly specifying a PAT from the key vault. The service automatically exchanges your Azure token for an Azure DevOps token at run time.
This example shows the ADO shorthand ({{ado://...}}). The service exchanges your Azure token for an Azure DevOps token at runtime, so you don't need to store a PAT in Key Vault.
$schema: "1.0"
tasks:
- name: git-clone
description: Clone this repository into C:\workspaces
parameters:
repositoryUrl: https://dev.azure.com/example-org/MyProject/_git/example-repo
directory: C:\workspaces
pat: '{{ado://example-org}}'
The Dev Box Visual Studio Code extension and Dev Box CLI don't support hydrating secrets in the inner-loop testing workflow for customizations.
Authenticate to Azure resources with service principals
Service principals let you securely authenticate to Azure resources without exposing user credentials. Create a service principal, assign the required roles, and use it to authenticate in a customization task. Hydrate its password from Key Vault at customization time using the existing secrets feature.
Create a service principal in Azure Active Directory (Azure AD), and assign it the necessary roles for the resources you want to use.
The output is a JSON object containing the service principal's appId, displayName, password, and tenant, which are used for authentication and authorization in Azure Automation scenarios.
Example: CLI output when you create a service principal. Store the returned password in Key Vault and grant the Key Vault Secrets User role to the Dev Center project identity so the customization can hydrate the secret at runtime.
$ az ad sp create-for-rbac -n DevBoxCustomizationsTest { "appId": "...", "displayName": "DevBoxCustomizationsTest", "password": "...", "tenant": "..." }Store the password returned above in a Key Vault secret, like this:
https://mykeyvault.vault.azure.net/secrets/passwordOn the Key Vault, grant the Key Vault Secrets User role to the project identity.
Now you can authenticate in customization tasks, hydrating the service principal password from the Key Vault at customization time.
Example: Download a file from Azure Storage
The following example shows how to download a file from a storage account. The YAML snippet defines a Dev Box customization that performs two main tasks:
Installs the Azure CLI using the winget package manager.
Runs a PowerShell script that:
- Logs in to Azure using a service principal, with the password securely retrieved from Azure Key Vault.
- Downloads a blob (file) from an Azure Storage account using the authenticated session.
Example: customization that hydrates a service principal password from Key Vault and uses it to authenticate and download a blob from Azure Storage. Store the service principal password in Key Vault and ensure the project identity has Key Vault Secrets User role.
$schema: "1.0" name: "devbox-customization" tasks: - name: ~/winget parameters: package: Microsoft.AzureCLI - name: ~/powershell parameters: command: | az login --service-principal ` --username <appId> ` --password {{https://mykeyvault.vault.azure.net/secrets/password}} ` --tenant <tenantId> az storage blob download ` --account-name <storage_account_name> ` --container-name <container_name> ` --name <blob_name> ` --file <local_file_path> ` --auth-mode login
This setup lets you automate secure use of Azure resources during Dev Box provisioning without exposing credentials in the script.
Example: Download an artifact from Azure DevOps
Download build artifacts from Azure DevOps (ADO) by using a service principal for authentication. Add the service principal's Application ID (appId) as a user in your Azure DevOps organization, then assign the principal to the Readers group. This step gives the necessary permissions to use build artifacts.
After you configure these steps, use the service principal credentials in customization tasks to authenticate and download artifacts securely from Azure DevOps.
Add a service principal to an Azure DevOps organization
To add a service principal to your Azure DevOps organization:
Sign in to your Azure DevOps organization, and open Organization settings.
In the menu, select Users.
On the Users page, select Add users.
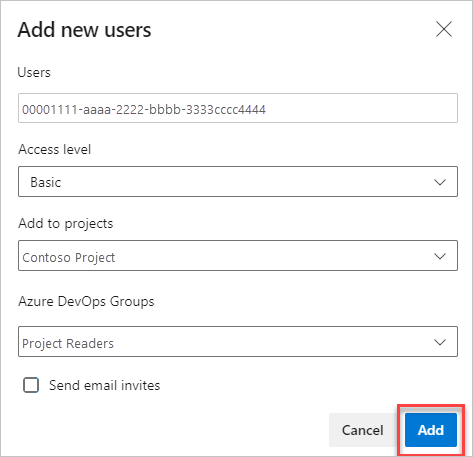
In the Add new users dialog, enter the following information:
- Users: Enter the service principal's Application ID (appId) as the user email.
- Access Level: Select Basic.
- Add to project: Select the project where you want to add the service principal.
- Azure DevOps groups: Assign the service principal to the Readers group.
Complete the process to grant the necessary permissions.
For details on how to add users to DevOps organizations, see Add organization users and manage access.